Solutions
Data Discovery & Classification
Discover unstructured data across all environments, creating a unified, continuous inventory that enables effective data classification
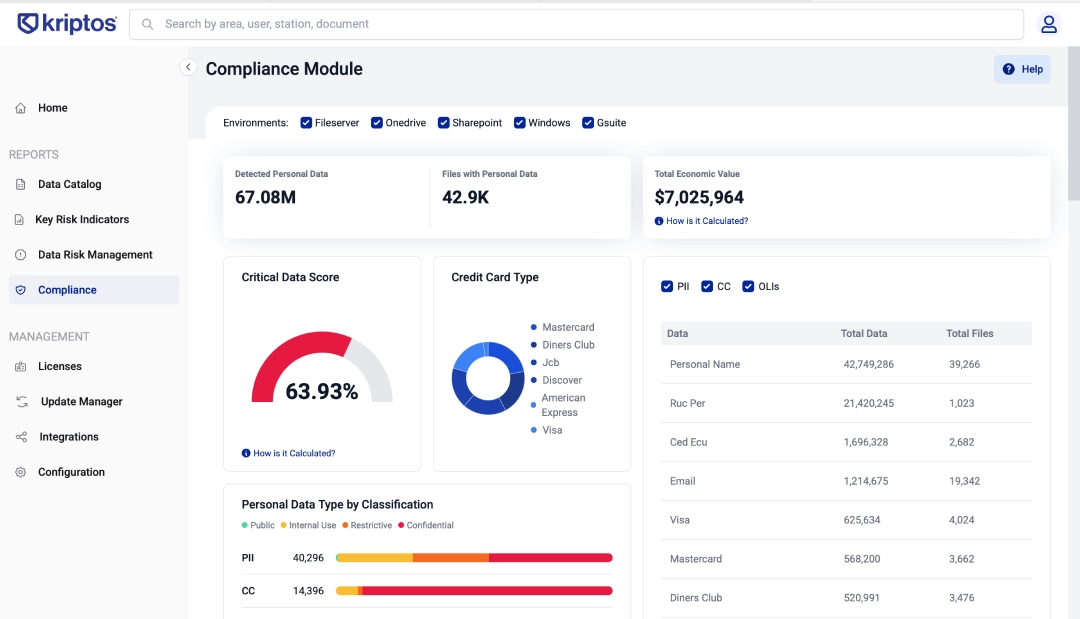
Data Compliance & Risk Management
Search, filter, and prioritize unstructured data with real-time context, metadata, risk signals, and compliance insights.
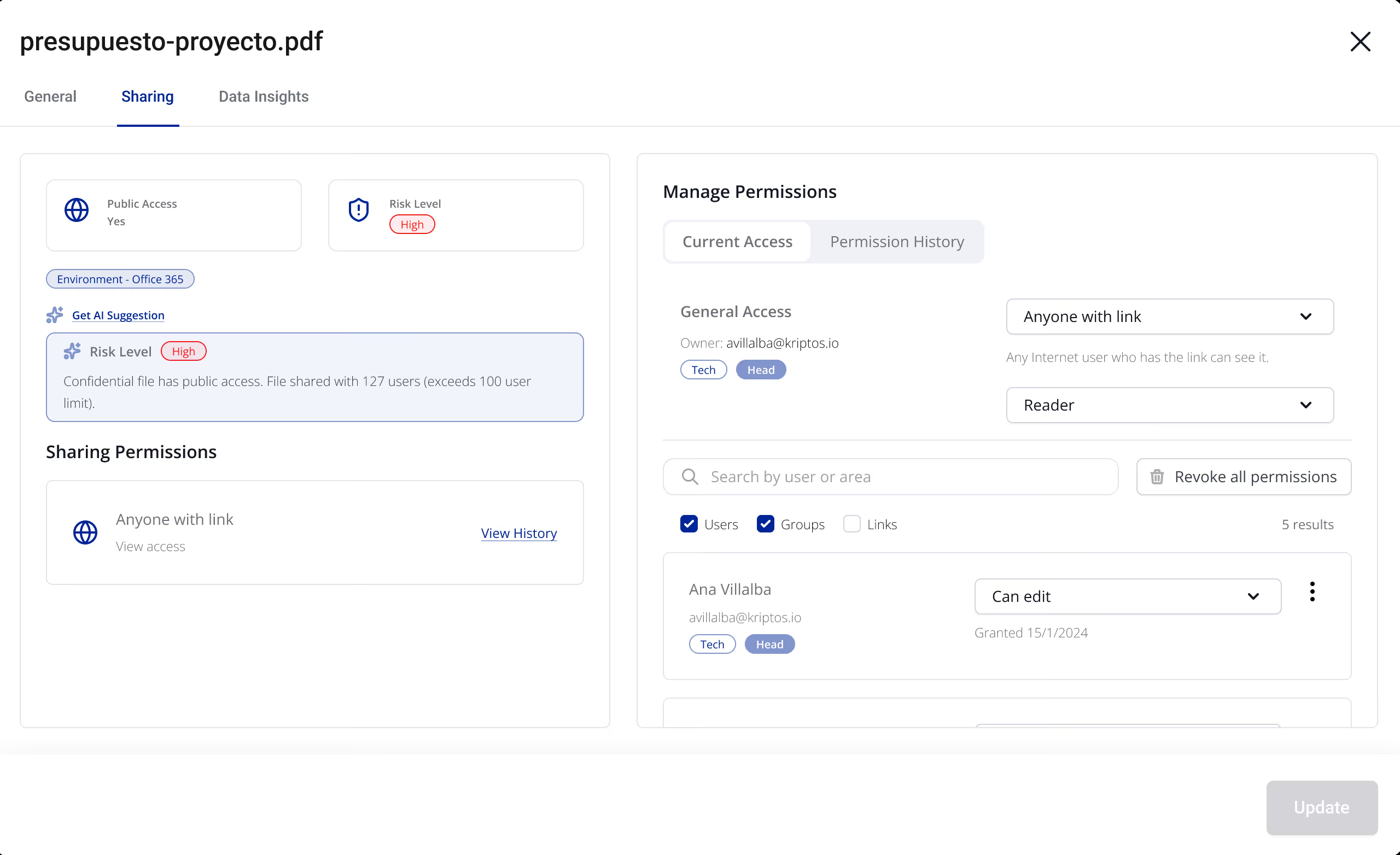
Data Access Governance
Control access to sensitive data by detecting risky behavior, overexposure, and remediating permissions with contextual intelligence.
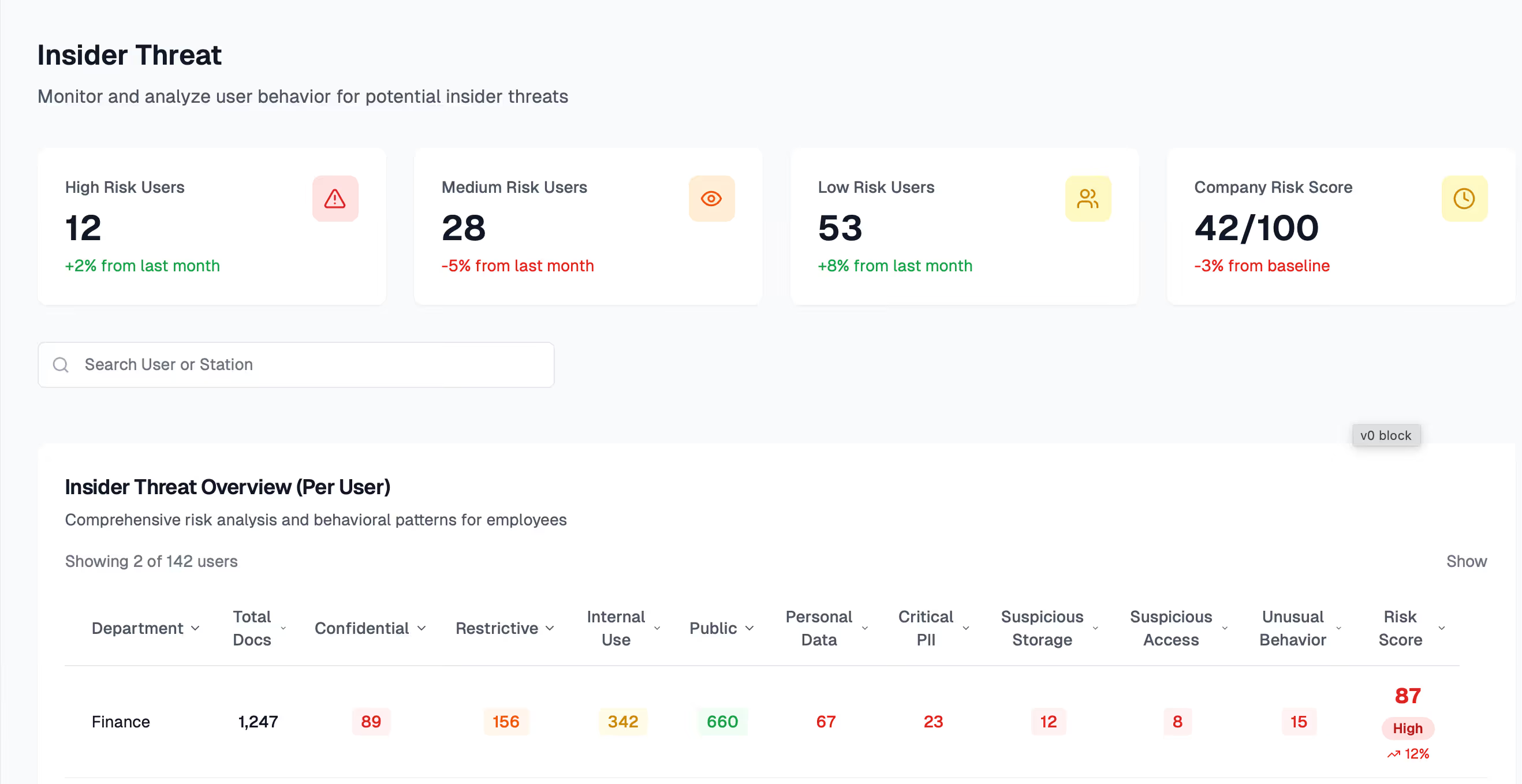
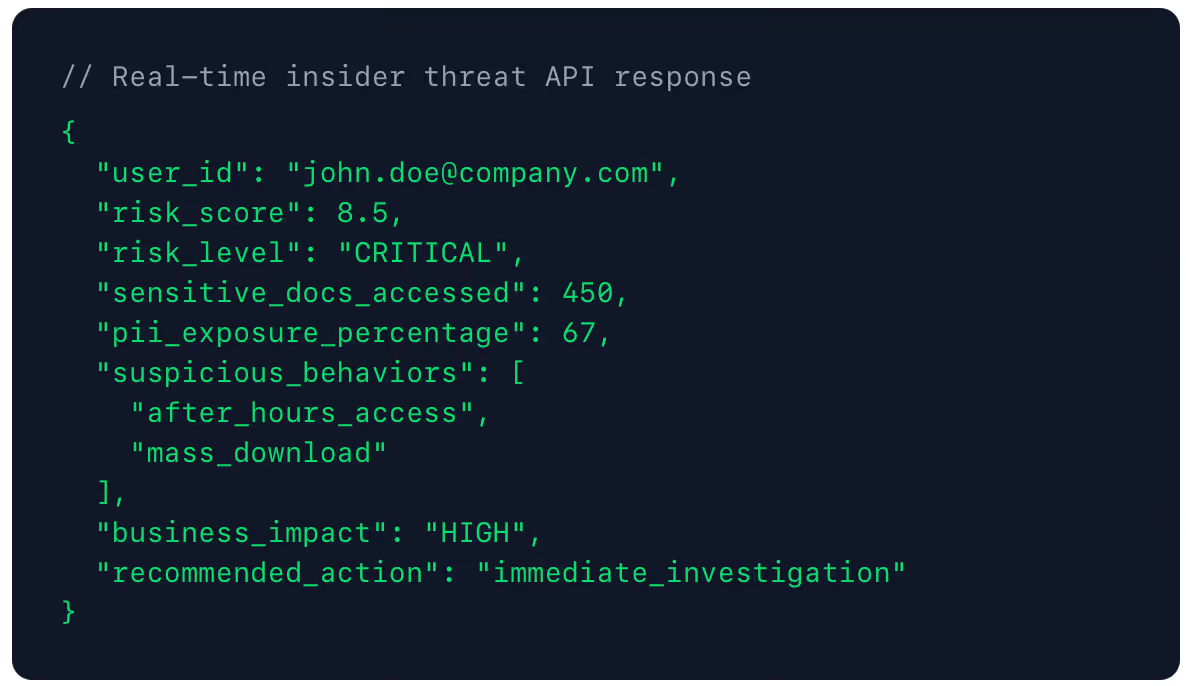
Insider Threat Management
Correlate user behavior with data sensitivity to detect insider risk early, enriching alerts with context.
Platform
Prevent Data Loss
AI-powered data classification that applies the right protection automatically, without manual rules or operational disruption.
Secure AI Adoption
Prevent sensitive data from reaching AI tools by identifying high-risk files and automatically blocking unauthorized sharing.
Secure Microsoft 365
Add intelligent classification that enriches Google and Microsoft tools to protect sensitive data beyond PII.
Ensure Compliance & Privacy
Turn data compliance into a strategic asset with streamlined audits, reduced regulatory risk, and built-in trust.
Secure Google Workspace
Provide business-aware classification and native Drive labels, so Google Workspace security tools protect sensitive data beyond PII.
Resources
ROI Calculator
Estimate sensitive data risk, classification effort, and potential leaks to make smarter, security-driven decisions.
Costumer Stories
Discover the future of data classification with AI and how companies achieve tangible security outcomes.
Source Center
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
Blog
Explore how Kriptos protects data and privacy through responsible security insights and best practices.
Company
About us
Learn about Kriptos’ purpose, values, and team behind AI-powered data classification, protection, and compliance.
Become a partner
Accelerate growth by becoming a Kriptos partner, gaining exclusive benefits, AI-driven data classification, and sustainable shared value.
Careers
Be part of our team and shape the future of AI-driven cybersecurity through meaningful innovation.
Contact us
Get in touch for sales, partnerships, or any questions about our solutions.
Privacy statement
Protecting your data with a strong commitment to privacy, security, and responsible information practices.