Soluciones
Detección, clasificación y etiquetado automáticos (DCL)
Automatice el descubrimiento, la clasificación y el etiquetado de datos para mejorar la seguridad.
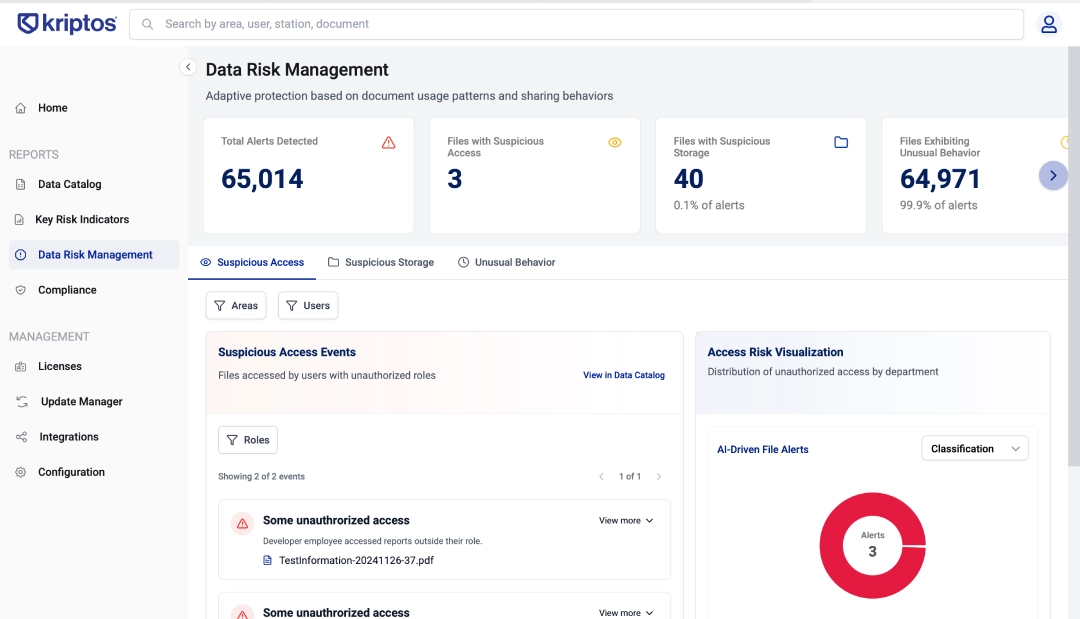
Gestión de riesgos
Optimice las operaciones con el descubrimiento de datos automatizado.
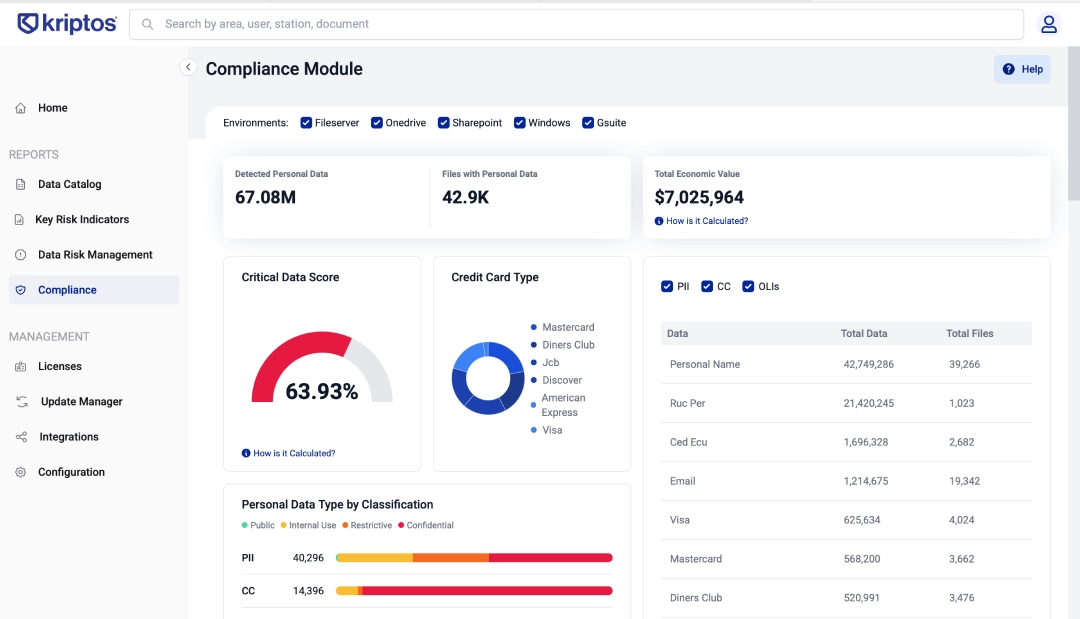
Auditoría y cumplimiento
Automatice los procesos de cumplimiento sin esfuerzo con nuestro software.
Finanzas y banca
Mejore su estrategia de seguridad de datos hoy mismo.
Plataforma
Producto
Descubra el futuro de la clasificación de datos con nuestra tecnología basada en inteligencia artificial
I.A.
Descubra la inteligencia artificial de Kriptos
Solicita una demostración
Programa tu demostración personalizada
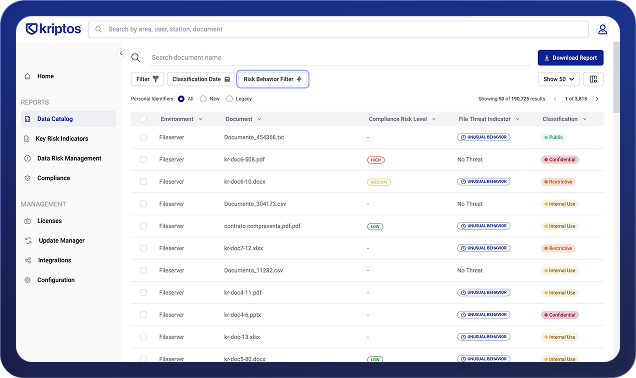
Panel de control de plataforma
Explore la plataforma web de Kriptos
Clasificación de datos e informe de riesgos (Calculadora)
Libere el poder de sus datos con nuestra calculadora interactiva
Recursos
Historias de clientes
Descubra el futuro de la clasificación de datos con nuestra tecnología basada en inteligencia artificial
Costumer Stories
Explore la plataforma web de Kriptos
Source Center
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
Blog
Explore how Kriptos protects data and privacy through responsible security insights and best practices.
Get a Demo